Either defence or defense, no-one can make out which of those.
About your LoD.
Certainly not the 3LoD kind; that idea has finally been shredded — unfit for recycling, nuclear waste (damages the brain if one would ever have believed in it).
But the real kind, that stand between a threat and a vulnerability. ‘a’ twice either singular or plural. Like e.g., real information security connoisseurs would know them, excluding the fakers (‘cyber’everywhere type).
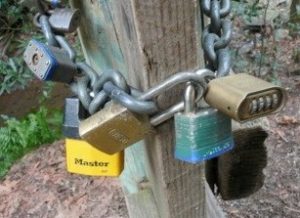
Where any additional layer will catch the errors, omissions and imperfections of the previous control / layer. Like you will have implemented in your infosecurity stack of solutions and controls. You know, this type:

How better be safe than sorry can one be ..!
Now, here’s the kicker: Any of these controls fails, the whole thing falls to pieces.
Which is perfectly like your information security is structured.
But … I can hear you think: “Indeed the picture is Stupid! The locks should interlink! And they should be of different types!” Yeah, like:
… Which has the very same problem!
Now, for ten points explain how you still think you got your infosec house in order. For another ten points, we would very much like to hear how you’d actually implement ISO2700x, COBIT even, or NIST CSF, or ISF, or … the whole range …, without making the above mistakes please?
[Edited to add: That’s how you do it: …?? Looks more like Compliance, making any use hopeless…]







