OK, herewith the final-for-now Part VI of the All Against All matrix-wise attack/defense analysis labeling. This time, about tactical content of … mostly, the defense matrix of edition IV.
Where I wanted to do a full-scope in-depth analysis of all the cells of Matrix IV. Not the sequel but the actual original defense posture strategy matrix. Because that was put together in a straightforward sloppy way anyway.
But then… I wanted to detail each and every cell according to this here scheme:
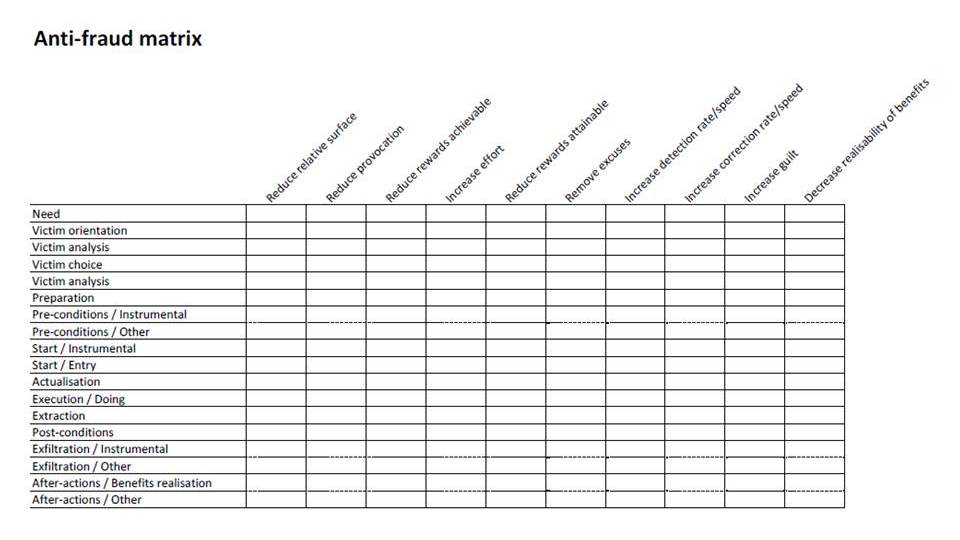
After further analysis along the lines of this here approach:
but mixing that quite hard, according to this previous post of mine (certainly the links contained therein, too) and a great many others contra bureaucratic approaches… but also mixing in the guidance of (not stupid compliance with!) the new one that at last, has quite some ‘user’ involvement in it. But still is based on both the top-down and the step-by-step fallacies a bit too much.
But it’s late and I don’t feel like the tons of effort involved. Yet. Maybe in a future enormous series of posts …
And should include references to OSSTMM here, too. Because al of the above, in the super-mix, will have to be checked and sensitized (is that the word for checking that it all makes sense?). Short of the word ‘audit’ where the respective profession (a trade, it is… at most, a role) has let us down so much. If only by the kindergarten zeal about ‘governance’ and ‘value’ – phrases so hollow (or circularly defined) that they’re not worth the ink (light) they’re written with, when used in the auditors’ contexts.
So, OSSTMM may help. By inspection where the rubber meets the road. And fixing whatever needed to be. Duct taping the last few bits, where the beautifully AutoCADded [anyone remember what that was (for)!?] frameworks failed in the machine milling. Or 3D printing, or whatev’, due to design failures due to requirements failures due to failures in common reason at the upper levels…
Now, with all the all against all posts (1 to 6 indeed), would you be able to advise Sony, and the others, how to be better protected ..? You should. Or re-read the whole shazam until you do…
After all of which you deserve:

[Cologne, of the massive kind]

















