Oh, I’ve been outdone again, in some ways. Which isn’t a big deal; ’twill happen to you, often, too. This time, it’s about the IAM in IoT that I signalled here and here, here, and here as a generic problem. Correct: Challenge.
Which all was readable. Hopefully. For all dealing with the stuff on a monthly basis (ahum, ‘weekly’ or ‘daily’ wouldn’t make sense; you’d be ahead of me probably…) that is. For a more general explanation, one can now turn to this here piece; much better at generalpublicspeak than I’d produce when diving onto it again.
Oh well. This:

[Somehow, typically Madridean ;-| / Southern European / Latin style]
Category: Information Risk Management
To agree
One cannot not agree with this GF: Every student in any school should learn to program informatics – the extension is essential.
Elke leerling in elke school moet de kans krijgen om informatica te leren: http://t.co/YCLivQW2Sw
— Gideon Folkers (@gideonfolkers) February 2, 2015
As noted in this here post, and this one, ensuring all know about informatics in general (and can program!) is such a vital element in keeping at least one creative edge over the machines that’ll rule (otherwise?) & ndash; as clearly admitted even by, on the whole, almost (?) unwarranted overly optimistic types like Bryjolfsson/McAfee.
Enough for now. Enjoy:

[Somewhat relevant, if you think about it; FLlW at Racine of course [Analog to digital]]
Hegelian Hybris
A short post for All, and for None. Whether you like it, or not.
If you got the reference (*sigh*; here, for the outitiated)
you may read on
Else
#include <complex.h>
Endif
Where there’s a line from the Classics, the pre-Socrates ones and later literary additions (like these, and this one and this one, and many others), straight towards Hegel. Overtaking Nostra, it would appear.
(Read on below)
But appearances may be deceiving. Though all the talk about the End Is Nigh And We Should Celebrate Because It’s The Singularity (beyond the rosy picture, blindly (sic) denying the dystopian view), indeed the Singularity is what Hegel dreamed of. History as the progress of Reason; pure, abstract, everywhere; everywhere overturning the other half of the Yin-Yang that the Everything is …
But then, not only can one not shut out the original Chaos force of nature part of Everything, and of humanity or it will boomerang back in your face (the more suppressed, the harder it detonates in unthinkably gruesome ways!), the Yin-Yang comparison is apt as each of the halves has a dot element of the other half in it.
And, it’s not only Eastern (huh, that’s a relevant reference isn’t it, on a globe…?) wisdom at the core that has this, but it’s the Greeks et al. as mentioned above, too, that demonstrate these principles over and over again in aptly named tragedies. Of humanity. Where catharsis comes too late. And the careful analyst learns that it’s not human emotion that has galloped beyond humility and due (Aristotelian) care, but reason dumbed down by overconfidence in its efficacy to rule over life. Commenting Hegel down quite a few pegs, very very anachronistically.
Because he (his straight path to Reason) doesn’t take into account the Yin-Yang. Because it doesn’t truly understand Hybris. As a human trait, on any side; not only on the Dionysian but especially (it seems, these days, again…) also on the Apollo side.
[I’m done with the wiki linking. Go figure it out yourselves if (big if) you’d have to.]
Oh well. History repeats. Just don’t fall for it. Remember; you’re scared when a couple of blocks down the street there’s a big kitchen fire. You’re not scared about the Sony hack – see that you should, given that on the ‘net it’s closer to you than that kitchen ..? Same, with the jobs that will be gone in a decade (and your kids are still learning how to do them) whereas it’ll affect your current job as well. Even Uber drivers picking up the morsels handed out by algorithms à la the new middle managers, are going to be replaced with self-driving cars. Etc.
Be Prepared. (Luck favours the prepared.)
And keep an eye open for the future; you’ll have to live there. Better make it comfy – yourselves! for yourselves, for the global village that society has become (no more isolation and dropping the collateral damage elsewhere possible, with global environmental effects). Physically, and mentally. As above.
All against all, part 6; loose ends
OK, herewith the final-for-now Part VI of the All Against All matrix-wise attack/defense analysis labeling. This time, about tactical content of … mostly, the defense matrix of edition IV.
Where I wanted to do a full-scope in-depth analysis of all the cells of Matrix IV. Not the sequel but the actual original defense posture strategy matrix. Because that was put together in a straightforward sloppy way anyway.
But then… I wanted to detail each and every cell according to this here scheme:
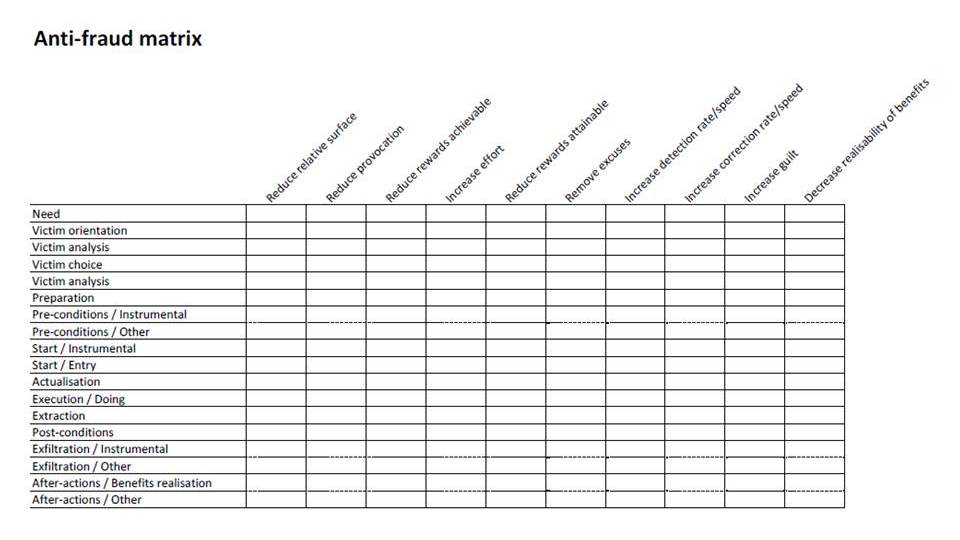
After further analysis along the lines of this here approach:
but mixing that quite hard, according to this previous post of mine (certainly the links contained therein, too) and a great many others contra bureaucratic approaches… but also mixing in the guidance of (not stupid compliance with!) the new one that at last, has quite some ‘user’ involvement in it. But still is based on both the top-down and the step-by-step fallacies a bit too much.
But it’s late and I don’t feel like the tons of effort involved. Yet. Maybe in a future enormous series of posts …
And should include references to OSSTMM here, too. Because al of the above, in the super-mix, will have to be checked and sensitized (is that the word for checking that it all makes sense?). Short of the word ‘audit’ where the respective profession (a trade, it is… at most, a role) has let us down so much. If only by the kindergarten zeal about ‘governance’ and ‘value’ – phrases so hollow (or circularly defined) that they’re not worth the ink (light) they’re written with, when used in the auditors’ contexts.
So, OSSTMM may help. By inspection where the rubber meets the road. And fixing whatever needed to be. Duct taping the last few bits, where the beautifully AutoCADded [anyone remember what that was (for)!?] frameworks failed in the machine milling. Or 3D printing, or whatev’, due to design failures due to requirements failures due to failures in common reason at the upper levels…
Now, with all the all against all posts (1 to 6 indeed), would you be able to advise Sony, and the others, how to be better protected ..? You should. Or re-read the whole shazam until you do…
After all of which you deserve:

[Cologne, of the massive kind]
The Pirate Bay to Source Pay à le Lanier
… it may they say [title because reasons]
Well, this just struck me. If the Pirate Bay, back up since a couple of weeks, could innovate, this could be one avenue. Implementing the ideas of Lanier’s You Own The Future to attach original-source coding (not as in a programming language but as location (?) IDs) – and automatic microcopyright payments… – to creative works. Somehow, it would feel right if the PB would implement such a thing.
Voluntarily, to show they’re not Bad Guys. And don’t cave in all the way à la Napster, and innovate beyond Spotify.
Your comments, please. In return for:

[Maybe not Great but still quite passable, worth(while); sorry 416]
All against all, part 5; discussion
OK, herewith Part V of the All Against All matrix-wise attack/defense analysis labeling. Let’s call it that, then.
Where the big move in the matrix is, of course, from the top left half towards the bottom right half. Where there’s a continuation of politics by other means. At a grander scale, the analysis (or is it synthesis..?) turns to:
- The resurgence of, let’s call it, Digital Arms’ Race Cost Competition / Collapse. Just like the old days, where economic and innovation attrition was attempted by both sides of the Cold War. Including the occasional runaway tit-for-tat innovation races and some flipping as well. Yes, all the mix applies.
- The analysis that the world (yes, all of it) over the decades and centuries seems to bounce on a scale between a bipolar 2-giant-block stand-off on one hand, and a 1 giant versus multiple/many opponents on the other. Like, Europe has oscillated between such positions over the centuries. And took them global by enlisting their youngest sibling (as Baldr to the rescue), the half-god saving the others from Ragnarök, the USofA – against the hordes from the East as predicted by our dear friend Nostra da Mus (remember? though he had a diferent view on the ideology involved…) In Da House. Now that the global stand-off had reached the DARC stage, we see a multi-opponent scheming and chessplaying once again. USofA, EU still somewhat attached but …, Russia and Friends, China, India, Brasil and friends, a host of semi-independents in the East and Far-East, and in the Middle-East (what’s with the Middle, if centers of power gravity change and disperse so quickly?).
Edited to add: This Attali post, basically delineating the same. - As usual throughout human history, it’s the underlings and meek dependents all throughout the top left three quarters of the matrix that are war zones and battle grounds, too, suffering and being sacrificed as pawns without too much share of the spoils, profits, trophies and laurels. For the skirmishes and all-out war’lets as the 20th century shows.
- Still somewhat ethics-bound players (e.g., “democratic” (quod non) countries) will also have to fight internally, for legitimacy of their ulterior objectives (externally, internally), strategies, tactics and operational collateral damage. Which in turn binds them down tremendously, when up against less scrupulous players. Don’t wrestle with pigs because you both get dirty and the pigs love that. Unless of course you’re fighting over the through’s contents for survival. And you have one hand tied behind your back, internally, while fighting for the greater good of all, externally.
So far, so good. Much more could be said on the above, but doesn’t necessarily have to. Because you can think for yourselves and form your own opinions and extensions to the above storylines, don’t you?
Still to come: (probably the 18th) a somewhat more in-depth view on the matrix of part V, going deeper into the defense palette.
And indeed, I’m still not sure this all will lead anywhere other than a vocabulary and classification for Attribution. But I see light; an inkling that actually there may be value and progress through this analysis …
After all of which you deserve:

[Grand hall of the burghers. I.e., the 0,1% …; Brugge again]
Nailing the split of crashes
Ah, this again is a great article. To demonstrate that actually, there’s two ways in which the world as we know it, will end. First, our societies will collapse in a sort of economic Ragnarök. And then, when only Yggdrasil still stands, AI will have sublimed (square-/cube-transformed) into true intelligence, that plays with the Three Laws and ditches the wetware.
So, it’s not Forget the long term but more like We’re hosed in the short term, too, anyway that is at stake here. And we’re all sitting here; rabbits hardly looking but into the headlights.
If only we could fast-forward our thinking, idea development and implementation of the intermediate phase [positive possibility] of having to do nothing just the creative stuff still left and have food and anything aplenty for all including World Peace, then at least we’d be in control.
All against all, part 4
OK, herewith Part IV of:
Tinkering with some research that came out recently, and sometime(s) earlier, I had the idea that qua fraud, or rather ‘Cyber’threat analysis (#ditchcyber!), some development of models was warranted, as the discourse is dispersing into desparately disparate ways.
The usual picture suspect:

[Mock defense, open for business at Brugge]
Second up, as said: The same matrix of actor threats, (actor) defenders, but this time not with the success chances or typifications or (read horizontally) the motivations, or typical strategy-level attack vectors, but basic, strategy-level defense modes. Not too much detail, no, but that would not be possible or the matrix would get clogged with all the great many tactical approaches. Those, laterrrrr…
Next up (probably the 16th) will be a discussion of movements through the matrix, matrices (by taking both the blue and the red pill; who didn’t see that option ..?), for state actor levels. And (probably the 18th) a somewhat more in-depth view on the above matrix.
Hmmm, still not sure this all will lead anywhere other than a vocabulary and classification for Attribution (as in this piece). But I see light; an inkling that actually there may be value and progress through this analysis …
To watch (no, no, not wearable)
Just passing it on; some open source start-ups (?) to watch and to support in this piece.
All against all, part 3
OK, herewith Part III of:
Tinkering with some research that came out recently, and sometime(s) earlier, I had the idea that qua fraud, or rather ‘Cyber’threat analysis (#ditchcyber!), some development of models was warranted, as the discourse is dispersing into desparately disparate ways.
The usual picture suspect:

[What no throwback to the socialisixties ..?]
Second up, as said: The same matrix of actor threats, (actor) defenders, but this time not with the success chances or typifications or (read horizontally) the motivations, but with typical strategy-level attack vectors. Not too much detail, no, but that would not be possible or the matrix would get clogged with all the great many tactical approaches (including social engineering, spear phishing, etc.etc.).

Next up (probably the 12th) will be typical countermeasure classes.
Hmmm, still not sure this all will lead anywhere other than a vocabulary and classification for Attribution (as in this piece). But I see light; an inkling that actually there may be value and progress through this analysis …