In particular, having fun the wrong way.
Remember, we wrote about how voice synth improvements, lately, will destroy non-repudiation? There’s another twist. Not only as noted, contra voice authentication for mere authentication (banks, of all, would they really have been in the lead, here, without back-up-double auth?), but in particular now that your voice has also become much more important again [after voice had dwindled in use for any sorts of comms, giving way to socmed typed even when with pixels posts of ephemeral or persistent kinds; who actually calls anyone anymore ..?], we see all sorts of Problems surfacing.
Like, mail order fraud. When hardly anyone still goes on a shopping spree through dozens of stores before buying something in store but rather orders online, of course Alexa / Home/Assistant / Siri / Echo / Cortana are all the rage. For a while; for a short while as people will find out that there was something more to shopping than getting something — but recognising the equilibrium that’ll turn out, may be in favour of on-line business, with physical delivery either at home, or at the mall.
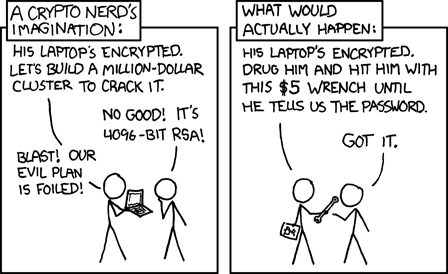
The big ‘breakthrough’ currently being of course some half-way threshold / innovation speed bump overcome, with the home assistant gadgets that were intended to be much more butler first, (even-more-) mall destructor second. But that second … How about some fun and pranking, by catuyrig just some voice snippets from your target, even when just in line behind ’em at Wallmart, and then synthesizing just about any text? When a break-in on the backside of your home assistant (very doable; the intelligence is too complex and voluminous to sit in the front-end device anyway [Is it …!? Haven’t seen anything on this!] so at least there’s some half-way intelligent link at the back) may be feasible per principle but doing a MiM on the comms to some back-end server would be much more easy even, and much easier to obfuscate (certainly qua location, attribution), a ‘re’play of just any message is feasible.
Like, a ‘re’play of ordering substances that would still be suspicious even when for ‘medicinal purposes’. Or only embarassing, like ordering tools from the sort of fun-tools shop you wouldn’t want to see your parents order from. Of course, the joke is at delivery time [be that couriers, DEA/cops, or just non-plain packages] — oh wait we could just have the goods delivered to / picked up at, any address of our liking and have the felons/embarressed only feel that part plus non-repudiability.
This may be a C-rated-movie plot scenario, hence it will happen somewhere, a couple of times at least. Or become an epidemic. And:
 [No mall, but a fun place to shop anyway; Gran Vía Madrid]
[No mall, but a fun place to shop anyway; Gran Vía Madrid]