Yup it’s time for one of those again. First, for the Dutch among us:
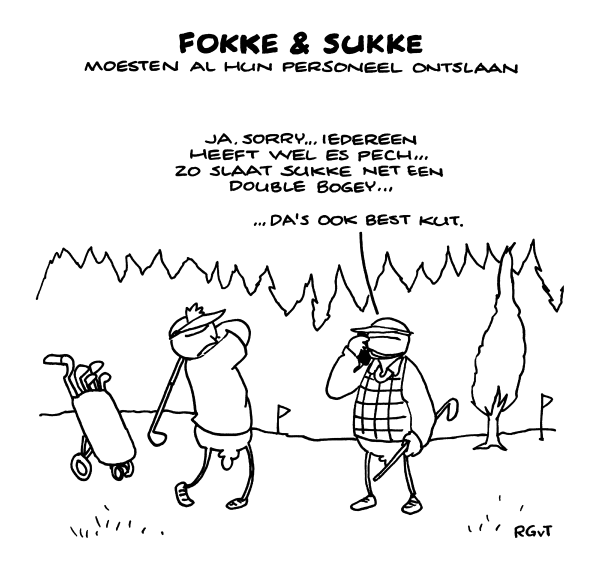
Then, for whiners in the 51st State of North ‘murrica:

[Get over it.]
Ah, just noted: A great many of you may have switched (or, c’mon don’t be a laggard or too late, will soon switch) to self-assessments of risks, even to the level of detail of data security (as part of information security, part of IRM, part of ORM, part of ERM, part of just-freakin’-perfectly-normal-or-are-you-kiddin’-me mundane run-of-the-mill average daily management of which ‘governance’ is the most preposterous windbag label).
Which is all very well, to determine at the shop floor levels, that apparently are the last hold-outs of actual business knowledge beyond the mumbo-jumbo of meddle management (sour joke intended), what the risks, and particularly also, Value of information (data…) processed might be.
But … You’d miss half or more of the picture, then. The value you attach to the info, may very well be what you’d be prepared to fork out to protect it (balancing estimated frequencies of intermittent losses versus continuous costs flying out the window), but you then forget that the attacker isn’t after the value you attach, but the value to the cracker. Which may be completely different. Think, e.g., Sony (and the many others alike): comparatively, there was hardly a nickel value in the ‘stolen’ (exfiltrated, or egressed since it was lying around so obviously) data from the Sony perspective. But the value was enormous from the hacker perspective — whatever the innocuous data was, the mere exposure was of such import that APT’ ing around apparently was worth it.
Now, how’zat (women have deliveries, men have Balls) for all the other info throughout your glocal enterprise/empire ..? Similar to same, I presume.
So, … what about the budgets to be made available to counter data theft/robbery/whatever comparison to physical-world expropriation you’d like to use? And still not trying to overshoot in comparison to the value you yourselves establish for yourselves by yourselves, or you’d run the risk (chance close to 1) of splattering any flexibility and usability under tons of ‘controls’ (quod non, BTW). But then, not protecting ‘regular’ data enough, might expose it too easily — which might be rational but will cost you, e.g., through EU data protection fines … ;-|
So, you’ll not only have to do the multiplication of this and this, but extend in other dimensions as well…
Oh well, the world gets more complicated every day… and:

[Your data protection; Noto]
Another consequence of the analysis mentioned before about answers flowing upward through infosystems and command and inquiries/questions flowing down: When the latter get viewed as anti-data or even anti-information, we see Information Theory in action.
Where without the creation of potential (difference) by an inquiry standing ready at, say, a sensor [abstracting for a tiny moment away from the complexity that could be in any sensor, assuming it a math point] to capture some data it may produce, the potential may not pull away the data created by a Heisenbergian creation (-by-measurement ..!?) of the data/anti-data pair. Leaving the anti-data, the uncertainty behind. Is this the creation, the maintenance, or the destruction of a Schrödinger’s measurement ..?
More operationally: In what way does this interpretation induce metaphoric (?) insight into the connection between physical world, ‘signals’ (as in Shannon and other Info Theory), and continuous (!?)/discretised sensor-data streams..?
[For once skipping the bullying of those not understanding the fundamental nature of the continuous/(math-)discrete divide]
Well, there’s also this:

[The gift of far-sightedness. SE Sicily you recognize of course]
Maybe @DARPA can elucidate … Why would anyone need four-legged soldier-helpers ..? First there was robodog, then LS3 that failed so may end up in your next indeterminableoriginmeat-burger. Next, maybe, a fully armoured full exoskeleton.
Which might do away with the humanoid innards in the near future (after that), losing some great many pounds of ballast (similarly, are drone pilots as physically fit as the bunch out there in the air on their weapons platforms ..?) and also losing a great deal in time- and otherwise (situational-closeness hence -fine-granularity) challenged ethical perspective. I.e., no weak knees anymore just shoot whatever moves.
But, back to the Helper idea: Why ..!? Why four legs, or even two ..? Instability assured… And Nature has donned animals with legs to get over tree trunks and boulders and the like yes, but maybe only because natural evolution only happens from the happenstantial last known good configuration not the clean slate ‘we’ now have when designing <anything that may silently carry some possibly superhuman load over rough terrain>.
Which is to say: Aren’t hugely more simple (contradictio semantics intended) machines possible with … even yesterday’s technology, that can do the same with no legs or completely different configurations of them? E.g., have ‘spurious’ legs on the back to be able to roll over (on purpose!) and still walk on? Tracks ..? Number Five is Alive! Silent ops can be achieved easily, just ‘invite’ some Rolls-Royce experts…
One only needs to add a gun of whatever size, and some Autonomous in the ops, and hey presto! A possibly much lighter than average soldier (easily stacked even more uncomfortably (possible?) in some freight plane for transport to the theatre) carrying possibly more, and a bigger gun a piece. No weak knees, or remotely operated — wouldn’t limited-autonomy ‘soldiers’ be able to be steered in platoons at a time from far away (and far away from anything officer-like or mayhem may ensue [disclaimer: once briefly was one]) and have an easy development of ‘grounded-drone’ armies.
After which, the Singularity takes over these all. Or just a bunch of the most capable.
Or, nearer future, some party being more than average removed from the artificial intelligence of the S i.e., some rogue general. How to stop such a guy (F/M) ..?
OK, you know where to drop the Challenge prize money, thanks. … … Or, the whole thing’s just a hoax to throw researchers of the too democratic inclination, off path since the research into the above is already progressing impressively… And:

[Hung from not hang over though that might (??) still apply to the operator; DC of course]
Met al die seminars en cursussen over de Wet meldplicht datalekken lijkt het wel of het meldplichtprocedurenaarbinnenrammen dé oplossing is voor al uw privacy-problemen.
Terwijl het natuurlijk niet meer is dan het perfect regelen van het naar buiten toe rondroepen van de totaal transparante schuld zodra (niet als) er iets misgaat.
Over het voorkomen dat beter is dan genezen (en dat is implementatie van de meldplicht-procedures nog verre van), horen we een stuk minder. Hooguit bij degenen die nu én zometeen de kous op de kop krijgen; dat alles anders moet terwijl het a. nu vaak al best prima geregeld is, b. zometeen niet beter zal zijn (feit bij voorbaat), c. a en b gelden binnen de kaders van de nu en dan geldende organisatorische belemmeringen van budget, tijd en wil van boven, om de zaken beter te regelen.
Het kan ook anders anders: preventief. Leest en ziet.
En ook:

[Zonder privacy, een saaie wereld …; Zuid-As maar da’s duidelijk]
When analyzing the Stork methodology for EU-wide federated eID- and authentication methods and technology, again one stumbles (rather, ‘ they’ do) over the bow tie of CIA, mostly C, controls. Too bad. Usually, ENISA(-involved) stuff is Great quality. Now, quite too much less so.
Which is too bad. To note, we already commented on the classical CIA rating (incl the bow tie fallacy) before. Now, the CIA seems to have something to bring to bear on CIA as well. Better study hard …!
Oh well …:

[Weaving transparency and stability, Cala at Hoofddorp again]
Close, as in no cigar yet (has the US ban on Cuban import been lifted already?).
But definitely, Risk Control Self-Assessments would, if carried out properly, be that major part of management’s daily (sic) chores that wouldn’t need annual get-togethers coaxed by outsiders (sic) but would be Business As Usual in operational practice. Maybe needing some periodic (weekly? monthly? certainly more than as now weakly annually) departmental review gathering but not a stage show as if this is the holy grail of business information flow. After which the ‘second line’ (as the back not even middle office function) receives the (right) info and acknowledges that the ‘first’ line has so much better sensors since they’re the first line par excellence, integrates the info into the upward report flow and reverts to fine-tuning the tools they provide to first-liners, and furthermore does … nothing. Second line is helpers, not dictators-by-soft-smothering. When it would turn out that all the high-quality hence qualitative (the reverse for quantitative) risk pics cannot be easily integrated into one pic, that’s too bad for the integrators but an appropriate (!) reflection of reality.
And if, on the other hand, first-liners need to be taken away from their actual productive work to sit in some song-and-dance by second-liners because it was so decreed by ‘governance’ levels (emperor’s clothes!), the very objectives will not be achieved. Since the ‘do something’ by deep-lying incompetence has lead to the wrong turn into a blind alley whereas the broad avenue (something like Younge Street) between wilderness and high (?) culture.
[I scheduled this post a couple of weeks ago for release in a couple of weeks but new developments seem to speed things up. For my many posts against Form over Substance … just search this blog for ‘TLD’ or bureaucracy …]
Won’t rant (too much) on; keep it to RCSA = BAU + quite some ε still, and:

[Distorted? Only your picture is, here for a change, by standing too close; true reality is not at the Edinburg Royal Mile!]
To close off [almost, since @KPN fraud themselves away from bankruptcy by series of outright lies to customers and tort] the year with a wild shot, ahead:
There is value in the information analysis in IoT, as described in Gelernter and many since, of the two-way flow of information. One, flowing up are information in the form of answers as aggregations or pattern matched tuples(ets); the other going down, being both commands and inquiries/questions.
This fits the IoT world snugly, and should be taken into account when developing IoTAuditing frameworks:
What we’re after of course in all of auditing — and this we consider self-evident or else go back to study auditing fundamentals, from agency theory! — is the controls that keep the quality of the back/forth i.e. down/up information flows within (client-!)required margins. No more! But be aware of who the client really is, not the one doing the actual paying. So, we may focus on the integrity of the information flows first and foremost, then the continuity (availability), and then confidentiality as an afterthought.
With neat break-downs to isolation, appropriate input/output buffering (anyone still aware of the difference between an interrupt and a trap? If not, take a hike and learn, and weep), integrity controls above all. And some thing on (establishing) the quality of aggregation and of the questions being pushed down — when the wrong questions get asked e.g. by lack of understanding of the subject matter (sic), as is so very commonplace in the vast majority of organisations today, the wrong results will turn up from within the data pool (reporting ‘up’wards).
And of course there’s the divide between
the operational world where actual business is done (either administratively in offices though one could argue (i.e. proof beyond recovery) that this isn’t actually doing anything worthwhile, or producing stuff), and
the busybodies world ‘above’ (quod non) that, which thinks (wrongly) to be able to ‘control’ and ‘steer’ the productive body, sometimes rising itself into the thin air levels of absolute ridicule (by) branding itself ‘governance’.
But do re-read all of last year’s posts and weep. But do also see the implications for variance in the integrity, availability, and confidentiality needs at various (sub)levels.
Twas bryllyg, and ye slythy toves / Did gyre and gymble in ye wabe
The brilly side has deteriorated, unfortunately, due to the great many that don’t avail themselves of the proper tools for the proper usage. [A CEO with you, is still a CEO]
No, really: when the ultrahyperventilating crowd decided to warp-speed run after the ‘any platform’ and subsequently ‘mobile first’ crazes (duly so identified), they forgot that when something’s meant to be visually interpreted, all the visual clues need to be clearly enough visible in the first place. Which goes better on a large screen than on a little one, unescapably. In the same way that the humongously dumbed-down ‘models’ that bankers and like w…kers use, are over by a stretch in their simplification of reality (and, stupidly, then taken as normative, prescriptive rather than descriptive in intent), visual interfacing for the mob-ile users are oversimplified to the uselessness side. Why??
Because [ I say so ] and [ hypes go that way ]. Lazy evaluation.
Which leads to: Not one size is too small to fit any, but all sizes are made fit for the content purpose. Maybe not even display when the deep message can’t be captured in too small a message display ..?
A bit deep, or dense, maybe. Hence:

[Circus, b/c you need bread; Oak Park old analog pic]

Voor sigaren bepalen we het profiel aan de hand van de criteria Smaak, Balans, Body, Sterkte, Aroma en Finish.
Voor Smaak pakken we het aromawiel erbij. Let wel I; wat u proeft of verwacht, kan gedurende de diverse fasen van het roken nog variëren... En let wel II; er zijn ook aspecten die nog niet zozeer als aroma staan aangegeven in het wiel, we denken aan termen als (ja de sigarenwereld is langzamerhand, helaashelaas US-, Engels geworden) zesty, tangy, floral, en earthy, of soms zelfs metallic. Lijkende termen die een combi zouden kunnen zijn van diverse aromas en papillaire en olfactorische/nasale sensaties en -tactiele invloeden. Hierbij komen termen als 'complex' uiteraard ook bijgepakt, om in dit geval te beschrijven dat er vele aromas herkenbaar zijn. Rustig roken, dat is niet alleen beschaafder en allerlei sigarenrokeneffecten-versterkend maar biedt ook meer kans om aromas te onderscheiden.
Balans is voor de hand liggend; of de zoete, zure, zoute en bittere tonen (OK, en 'umami'...) in balans zijn. Ja, ook bij een sigaar – al zal het meestal gaan over de balans tussen 'creamy' en 'spicy' en gaat het meestal mis door te veel bitter of te veel spiciness.
Body gaat over de volheid, in dit geval vooral te bepalen aan de volheid, dikte, dichtheid van de rook. Die ook een gevoel geeft; 'light' is als een licht bier, 'full-bodied' is als een rechttoe-rechtaan whisky of cognac.
Overigens hoort bij Body ook textuur, 'leathery', 'meaty', 'silky', 'creamy', 'soft', 'succulent', 'woody', 'chalky', 'dry', 'oily' en 'spicy'. Die dus net niet hetzelfde zijn als de aroma-indicatoren uit het wiel; soms overlappend. Niet handig maar zo is het nu eenmaal.
Sterkte is een wat eenvoudiger maat voor het nicotinegehalte van de sigaar. De topbladeren van een tabaksplant heeft meer nicotine dan de lagere bladeren – me(n) dunkt dat de topbladeren zijn waar de plant verder wil groeien en dus betere bescherming nodig heeft van de nico; lager is het wat ouder en 'expendible' dus ga je daar als plant niet je nico op concentreren ..? Waar de sigaar van gemaakt is, heeft dus invloed. Kan je meestal niet kiezen, maar wel proeven. Rustig roken is ook hier handig; om een nico-klap/duizel te voorkomen bij het opstaan.
Aroma dan, vervolgens. Ook hier kan het aromawiel worden ingezet. Vreemd genoeg is het moeilijk de aromas te bepalen als we zelf roken; iemand anders' rook kunnen we beter analyseren. Of we blazen de rook door de neus uit ('retrohaleren'), dan hebben we wel de volle verfijning (ga ik vanuit, lezer!) van onze neus ter beschikking. Bedenk bij het 'benoemen' overigens dat we veel meer uit ons geheugen putten, qua eten en drinken!, dan we wellicht zelf(s) denken. Dus rare smaken herkennen is niet raar.
De Finish ten slotte is kort of lang, naargelang de aromas lang op de tong (sic) blijven hangen. Milde sigaren zijn nogal eens kort – hetgeen niks zegt over de complexiteit, overigens. Hierin zit ook de reden om een zwaar (sterkte)kanon na een milde te nemen, niet andersom.
Als het gaat over de champagnes en hun profielen, pakken we er de (echte en semi-)klassieke wijn-analyses bij die we allemaal wel kennen; onderscheidend in [Hier verder. In ieder geval https://www.wijnwinewein.nl/hoe-proef-je-wijn/ en aromawiel + zuurgraad/tannines/body(viscositeit/alcohol/tannines/smaakintensiteit/mondgevoel)/afdronk + Aanzet/Zuren/Zachtheid/Tannine/Body en alcohol/Afdronk/Smaken dus de aromas bijna-los van structurele criteria. Dan de smaken matchen met die van sigaren, of niet; Klosse's overlap/contrasten erbij halen en dan verder. En toespitsen op champagnes... pak het smaak-plaatje van het CIVC erbij!]
Dear reader; bij deze dus de waarschuwing dat u vanaf hier (?, inderdaad, echt niet alleen hier) serieus te lange zinnen tegenkomt.
Ach, daar ben ik me prima van bewust, mijn hele blog is immers ook een poging tot schrijfoefening in alle facetten. Sommige posts daar blinken uit door korte zinnen en ellipsis; ook deze pagina is opgesteld als tegenwicht. En ik vertrouw erop dat u dat gewoon doorlezend aankunt.
Als voorbeeld: Oplettende lezers zullen opmerken dat onderstaande waar het uitweidingen achter links naar andere pagina's betreft wellicht beter met behulp van OnMouseOver's, alt-tekstblokken of andere tags per pop-uppable item zou kunnen zijn geïmplementeerd maar ik heb het zo gekozen en ik kan best komma's toevoegen in deze zin maar ook dat heb ik achterwege gelaten zonder de leesbaarheid of de begrijpbaarheid in het gedrang te brengen.


Inderdaad, het ontwikkelde, ik schreef, een en ander vanuit een voortdurende, voortgaande research. Na zoeken in het wilde weg algemeen, navraag bij het Comité (iv) Champagne, een aanvullend zelfzoeken met Google Satellite én Street View zowel rond de officiële als in het algemeen, kwam ik tot de Lijst Van (uiteindelijk) 84. De en passant gevonden kaarten leidden tot enige aanvulling. Toen kwam ik Weinlagen.de tegen en tsja dan ben ik niet meer te houden qua sys-te-matisch alle streken én plaatsjes af! Hoewel, ... in onderstaande tabel heb ik maar niet meer voor ieder stuks de Street View erop losgelaten of onderstaand ingevuld. Terwijl ik er vanuit ga dat dit alles nog aanvulling kan krijgen ... Les Clos Inconnus zijn uiteraard zichzelf.
De gangen kwamen al zeer onregelmatig door, en met andere tafels die uitliepen en/of (weer) bijtrokken, tot zeer ver inhalen zelfs, tot gang 6 van de 7 tachtig (schrijve: 80) minuten op zich liet wachten, ondanks diverse malen navraag. Waarna het nauwelijks-opgewarmde pompoen met koude polenta bleek te zijn; "dat hoort zo" ammehoela. Nee, het niet-koude nagerecht erna hebben we niet gehaald; we zijn opgestaan en weggegaan. Die zien ons nooit meer, zeker omdat de bediening ook Zwak was (gangen aan verkeerde tafeltjes serveren want die waren al twee gangen verder), etc. En balsimaco-saus dus, 'et al.'...
Huh, da's écht voor de Insiders..? Inmiddels wel toegestaan als aanplant, maar nog zo'n drie tot tien jaar onderweg voor er de eerste re-de-lijke wijnen van kunnen worden gemaakt en dan is het nog maar afwachten. Je weet het niet van tevoren hè, met zo'n non-Vinifera druivensoort..! En dan had je Floreal, Artaban en Vidoc nog niet gezien. Die mogen (in de toekomst) ook... En dan is het Comité Champagne ook nog bezig met kruisingen van de Top 3, Arbane, Meslier, en Gouais. #feest
En dan komt hierna een nóg spectaculairdere outsider: Chardonnay rose Rs, minder dan een kwart voetbalveldje aanplant...
Mineraliteit verdient een aparte behandeling; vanuit het idee van 'huh er zit echt geen mineraal/steen in je wijn en lik jij aan stenen-dan'-versus-'toch proef ik die sensatie en Ja' tot en met de abstracte benadering van een kennelijke associatie van een gewaarwording als hier, tot een synthese op de as 'bodem-microbiologie'-in-combinatie-met-'feitelijke chemie'. Want, jawel, fenylmethaanthiol zorgt voor vuursteen / aangestoken lucifer, in combinatie met benzaldehyde (uit 'hout') en waterstofdisulfide (uit reductie; en beide uit bepaalde gisten!) leidend tot Vuursteen-herkenning, versterkt bij anorganische ammonia bijvoorbeeld. Vuursteen is geen 'mineraliteit' maar daar wel belangrijk onderdeel van. Dus Ja, er zitten wel degelijk chemische stoffen in (niet alle gelukkig) wijn die een sensatie veroorzaken die op mineraliteit lijkt. Zout, uiteraard, ook, (niet meer maar wel) vaker dan we denken! Alles tezamen een uit-ste-ken-de reden om te spreken over herkenning van Mineraliteit in wijn. 0-10 en een penalty tegen voor de geo-logen.
Laherte Petit Meslier in the tasting round
Yes @laherteaurelien makes a monocépage of this one. Great Meslier it is:
The golden colour would suggest something dosée, but look closer and you notice a hue which points to slight bitter influences. And indeed, on the nose we get a whiff of smoke, certainly straight after the pour; quite an opportunity to use the word ‘empyreumatic’... Did I mention Meslier already? One to one it is. But nothing referring to your cooking qualities; it’s more like a distant secondhand puff of Belinda – I’d not suggest you buy that for comparison; trust me as smoker it’s trash but as Meslier aroma it’s excellent full stop. Crispy dry cigar smoke fits better.
Certainly, since this all is followed up, much more persistently, with quite some mature lemon and a whole slew of herbs and spices notes. It smells like a merry-go-round of eucalyptus, dill, thyme, spearmint, soft mint, basil, anison, verveine... wormwood even; those that know génépi, find it here, too.
The first sip jumps in with a most delicate mousse, a sensible but not too fatty mouthfeel, nicely balanced with lemon dominant in combo, and ginger/pineapple/mirabelle and dry lemon rind flipping back and forth. In the remarkably long finish, the rind does a gentle cleanse.
But I couldn’t find any cardamom that some mention, nor cocoa or coffee. All in all, in cocktail terms it would fit in the range of the French 75 and a Fleurette.
I’ve tried a little bite of camembert, but you shouldn’t. The bitter of the wine is lost but notches up in the cheese, which tastes odd. The fit with lightly aged Comté or same-Gouda is perfect, however. Sushi should work, too, if with a suitably subtle pinch of wasabi, no more – harsh coriander, algae, chervil, wasabi as such weren’t in the nose.
In summary: All of you should have a taste of this one, or one couldn’t be trusted on champagne connoisseurship.
[Degorge 12-2021, hence the progressed maturity]
Links:
https://maverisk.nl/de-forgotten-four/ for Petit Meslier
https://maverisk.nl/champ-sigaar/ on the cigar smoke angle
https://maverisk.nl/geneprima-spul-hoor/ on génépi
https://maverisk.nl/mirabelle-wil-iedereen-welle/ on mirabelle
@champagnepascalmazet make quite an interesting range of wines, fully certified bio since 1980. We tasted the Cuvée Originel bottling of 2014, for its 35% Pinot Blanc of course; interested to learn how such a Forgotten Four lead, with the three Usual Suspects trailing, would work out.
‘Splendidly’ is the answer.
The gold is striking, the nose is suitably complex. One gets mint, cucumber, cornichon tartness (I mean, the true kind of https://www.kesbeke.nl/) and some olive.
On the palate, it switches to agrumes-allsorts. Yuzu, lightly pre-ripened apricot (yes there’s acidity in there), sparkling grape (ah.) and a hint of almond already. This slowly develops into lemon-grapefruit on the one hand, and yellow curry / pineapple on the other, with a tangerine almost orange'y element integrating both sides. I’d say, there’s a marbling of mirabelle (in Dutch: https://maverisk.nl/mirabelle-wil-iedereen-welle/) running through it as well.
‘But’ overall it certainly is far from flubby (the 3g dosage having turned into the above, no sirup) or acidic. The quality of it all, and the light oak touch, twist all the richness back towards the freshness of citrus zest. And did I mention the mousse is still there, slowly releasing?
Towards the lingering finish, this all persists in a extremely well-balanced acidity and a hint of minerality and sophisticated bitterness.
Am I happy to have another one of these standing ready
Marie Courtin Présence
I bought the @ch_mariecourtin for the 1/3 Pinot Blanc (of course: https://tinyurl.com/ForgotFour !). High expectations, exceeded.
First off, the yellow-golden almost amber colour would promise some sweet almost creamy elements. But with a delightfully tingle from a fresh mousse, and a light bitter-tartness in the nose, the picture turns around completely. There’s Mirabelle ..! [As per: https://tinyurl.com/Mirabellepg]
The palate is perfect; not too much mousse so the real ‘wine’ taste is clear, and the Mirabelle keeps on coming. The mouth feel overall is well-balanced, and includes a soft minty/dill side with the lemon (plus some bittersweet orange even), moving into the grapefruit area and then the mirabelle’s back again. The very long finish has the mint/dill combo again, and an inkling of sugar. But with zero dosage, that’ll be the Chard and almost certainly the Pinot Blanc waving goodbye. Throughout, there’s a slight undertow of pickled cornichon (Amsterdam style; what else?)
All in all, it’s a wonderful demo of what Pinot Blanc can bring; lifting the Chard from its average whilst pulling itself up into high performance. Merging the best of both into Something Else of a great wine. This being a zero dosage, zero sulphur added, zero intervention wine, it also proves that ‘natural’ wines need not be f(l)unky. But on the contrary, one would hardly be able to tell.
The Présence is course material in so many ways. Am I happy? Well, not with six other dwarfs but yes, very much so.
The @champagne_gruet Cuvée Arbane …
𝘚𝘰𝘮𝘦𝘵𝘩𝘪𝘯𝘨 𝘌𝘭𝘴𝘦 entirely!
100% Arbane yes. Which brings a freshness too long lost. Reminds me of the bone dry styles of yesteryear, in a good, rather great way. Chalky without dust, minerality without flint. A wonderful conversation starter, on the good things of life.
With a fresh and quite light, lemon-white colour through which a very fine and persistent mousse promises delight. Then, on the nose, one gets a first whiff of floral notes; jasmine, elderberry, rose – followed by zingy but ripe lemon. When allowed to mellow in the glass (or a day in the bottle), the lemon slowly brings along some grapefruit, pineapple and (dry white) melon. All within measure, refined, nowhere too in-your-face’y.
The mouthfeel is brilliant with the mousse playing its role to keep the very well balanced aspects all quite light. The dosage is hardly noticeable – from the taste of it, one would estimate 2g. max, and notes of soft white peach, light albedo, with a very long finish on the thyme/mint/dill spectrum with the albedo bitters lingering on.
Would work miraculously with e.g., flounder with serious sauce and herbs, swordfish with almond crusting, maybe tuna or mackerel, or white meat.
Saw a score somewhere of 91/100, but that's too low.
Buxeuil doesn’t have any Arbane of its own (in production), but with this Gruet wine, it has a flagship.
Arbane being at only 0,018% (yes, percent) of Champagne’s acreage, this cuvée highlights the 'need' (want!) for quite an extension of that.
Tasting the Pinot Blanc champagne of Gruet of Buxeuil (@champagne_gruet). That’s right, a pure-bred PB champagne. (Be sure to pick the right one, at https://www.champagne-gruet.com/)
And it is a treat, indeed.
In the glass, we have a very fine mousse, well-integrated - it continues very, very long and doesn’t just give a one-off foam layer – through a pale gold, slightly varietal-typical PB wine.
On the nose, the typical character come through immediately, including a slightly fluffy air of white flowers around light tangerine / (white) peach / mirabelle, and a core of lime – keeping nicely short of being bitter.
The mouthfeel is light, but not fleeting. One gets beautiful straight near-ripe lemon, a waft of mint with white blossom, and some white pepper towards the back. Add to that lemon white skin with edges of red grapefruit.
Mind you; I had kept some for a second tasting, and four days (suitably cool storage) after opening, all this was still as fresh. No ‘dosage plays up after too much air’ or so; great.
A top recommendation, this one. If only to keep the Forgotten Four Cépages alive, as they deserve, but also for sheer tasting pleasure. Or ‘the trick one’ at a tasting experiment. Or for an apéritif or with whitish seafood (if not to lime’y or salty).
The Réminiscence 100% pinot blanc brut nature by @champagneericlegrand via @jeromeschampagne. Supposedly off 65+yr old vines, but one would be hard-pressed to tell that by the wine. What delicious freshness!
For a start: What would one expect from a pure PB champagne? Subtlety indeed.
It starts with a new capsule (for me, to further fill my https://www.deknudtframes.fr/en/catalog/product/s65sz2-/frame-in-black-for-champagne-caps which only applies to *different* capsules I tasted *at home*) – under a muselet to duly impress. After a good whiff, one can immediately pick up the something-different of this one. The first 80% is most clearly artichoke with some mint; not very strange since we just made such a dip for (neutral) crackers five minutes before.
After which, with careful nosing/tasting, we get a white-floral element with traces of almonds and yes even a hint of vanilla and the slightest of dried yellow fruit. This continues in the long developing taste, clearly adding ‘a point’+ ripe lemon (citron), with the etheric element slowly (very slowly) fizzling out. Can I say ‘retronasally’ there? As it tactilely *feels* that way for sure. Add some vanilla points in the long after.
All in all, a thing to be savoured. And, let’s promote these ‘forgotten four’ champagnes! Away with the factory work! (One suspects the 24x range by some famous grand marque points in the right away direction, too, qua hyper-mass production orientation.) The more sure we have of being able to choose to never have to taste a same champagne ever again in one’s lifetime. *If* one would want to – wines like the Réminiscence make one still would want to return often. Extend the plantation!
Another round for Gruet of Buxeuil (@champagne_gruet) – The Cuvée des 3 Blancs (as here)
With its matte gold, almost amber appearance and very fine mousse (hardly foamy but lingering in the mouth for a long, long time), we'd expect the Pinot Blanc to dominate over the Arbane and even Chard. It does. A little. But, as assemblages go, only a little; I'd rather say one can identify the PB by its gently soft but full agrumes/mirabelle character but there's a lot of exquisite light flowers – hawthorn – and herb'iness – in the sage, rosemary corner – already in the aromas. Would that be the continuum of the Arbane and Chard?
If one would want to take it analytically.
Savouring, one would enjoy the all-round calm structure, with a medium to full mouthfeel (nothing sticky). And just the image (?) of a surprisingly light white wine with lots of mature grapefruit, lemon and a slice of lime. From which the little bitter note lingers on in the back, most pleasantly refreshing, nothing astringent or harsh. Overall, certainly not chalky bone dry but a hint of mango.
Would I pair this all with food ..? That would be a. hard; a very careful cheese selection might do, b. interesting, to see where the flavours go (see below), c. not necessary, it's a wonderful treat on its own.
This, in a series of Forgotten Four tastings, as per this 'research'.
And the (aubépine and) mirabelle note, Gruet themselves also list. Nice, yet another example of that great aroma.
Plus, one of course has e.g., this and this book, or quite a few others, already..?
Of boek. Hoewel er een beperkt aantal boeken is dat ik hoog heb, zit er niet een[1] bij die nou net op het onderdeel dat mij respectievelijk interesseert, het α tot en met ω heeft. Waar-om en waardoor ik juist de verdere research wil/ 'moet' doen...
[1] Nou ja, deze komt in de buurt...
Jazeker! Zoveel is zeker: Voor bijvoorbeeld de Fransen is dat een volstrekt normale karakterisering. Het gaat dus niet om NaCl uit een Jozo-vaatje... Eerder "off-vuursteen"; denk ook aan de regio van hints in de verte bij wit-peperigheid en magnesium in de buurt. Niet vreemd, als oesters zeer rijk zijn aan zink (sic), ijzer, calcium (dûh) en selenium. Sommigen in NL zeggen dan dat je geen 'zout' of zelfs maar 'zilt' mag zeggen. 1. Van wie niet ..!? 2. Waarom niet ..!? 3. Dat is toch voor zéér velen de beste karakterisering – niemand beweert dus dat er keukenzout in uw wijn zit en iedereen weten dat de karakterisering losstaat van enige bewering van objectieve chemische samenstelling anders zouden we wijnaroma's héél anders beschrijven!
Of zelfs Philpatrick het moet niet gekker worden ... Dus denk niet dat de spellcheck op hol sloeg.
De Cuvée Métisse, noirs et blancs oftewel 80% PN en, jawel, 20% Pinot Blanc, wederom een assemblage met een van de Forgotten Four. Brut nature dat houdt het puur, klaargemaakt bij de BV Val du Clos dan nemen we ook een verre hint daarvan mee. Van Champagne Olivier Horiot, MeB juli 2020, dégorge 16 jan 2023, grotendeels oogst 2019 plus nog een scheut uit de Réserve Perpétuelle die op eik wordt gehouden – ja ik kwam 'm in een coin oublié tegen maar prijs me gelukkig. Quelle belle ouvrage! Als u denkt: Da's een nogal technisch verhaal – dan is dat juist maar het proeven is gewoon een onbekommerd plezier. Het begint uiteraard met de sprankelende licht-amber kleur en een neus met het lichte bittertje, denk aan het dille-thijm spectrum, van de Blanc. Terwijl dan de eerste smaak van de Noir komt. Hoewel licht door de jaren, en dat pufje bitter komt er snel weer bij. Rijpe-appelzuur, heel lang gematigd door-coastend verdund citroensap met in de verte mango en met witte zest erboven zwevend. Maar wel in complete balans, niet vlak of zo maar juist met transparante diepte. Toen ik er een hapje net-nog-niet-compleet-rijpe ananas(kern) bij nam, was dat een moeiteloze, zowat volledige overlap. Later komt er een onderstroom(pje) van iets dat neigt naar kruiden door de mond. En nog steeds met zeer fijne bulles, by the way; verfrissend zonder prikje. In termen van verwachte aroma's zou ik eerder tussen Chard en Meunier op pad gaan van jong naar iets voorbij het midden, en zeker niet te ver naar de rijpe complexe PN-hoek zakken. Al met al een 'opulente' wijn die verrassend jong van geest is (gebleven). De PN is meer steun dan leider in het geheel; prima! En de PB viert z'n vrijheid om te shinen; uitstekende reclame!
5 Sens: De Oogst-2017, MiB 24 juli 2018, Dégorge 12 mei 2023 ja zo exact, met nul dosage voor slechts 1320 fles plus 90 magnums. Van 5 verschillende terroirs, oude stokken van 5 verschillende cépages – PN, Chard en Meuier, en dus ook Arbane en Pinot Blanc; langzaam vergist en opvoeding sur lies. Dat geeft volgens de makers de vijf (jawel) elementen Water, Aarde, Luchten Vuur – en l'Esprit! Wederom een assemblage dus van Olivier Horiot (op @horiotolivier) met Forgotten Four, klaargemaakt bij de BV Val du Clos dan nemen we ook een verre hint daarvan mee. Zo, dan heeft u de data gehad. In termen van aroma's als op de vaste plaat gaat het alle kanten heen, waarbij we ook (laten we zeggen 'traditionele') Chard- en PN-aroma's tegenkomen. Maar niet te uitdrukkelijk. Om het op een rijtje te zetten: De kleur is vol maar licht goud; De mousse is heerlijk, (nog) ruimschoots aanwezig maar zeer fijn; In de neus krijgen we eerst rozenblaadjes en een tikkie mango, maar zo nu en dan ook een zweem ziltigheid ..? Een ander zou het ook witte-peperigheid kunnen noemen. Sommigen vinden dat Arbane meidoorn en anjer geeft; nou ja dat kan ik begrijpen maar pikte ik niet op. Noch wat appel en kweepeer, dat gewicht trof ik minder: Het volle mondgevoel zit stevig in de citrus-hoek. Denk aan lauwwarme, (over)rijpe citroen met een beetje suikerrijpe peer en (geblancheerde) ananas, op het mirabelle af maar wel met een los zwevend zuurtje dat eronderdoorlangs komt zweven, inclusief een puntje venkel/dille. Ik denk dat hier vooral de wat rijpere Pinot Blanc om de hoek komt kijken. Maar al met al wordt het nergens te zwaar; de wijn blijft gewoon helemaal in balans; De citroen is de core der (talrijke) caudalies; zelfbewust maar niet zwaar. Nou ja, als eindconclusie; deze zit op het niveau van een lichte montbazillac of sauternes met mousse..! Werkelijk heerlijk. Voor zover er wat bij moet worden gehapt, zou ik zeggen: Niet te licht, niet te dicht op de sla/Brillat-Savarin-hoek, of te kale zilte oesters. Eerder oesters met enige bewerking, zou ik zeggen. Als per deze – en een geel- of roodschimmelkaasje kan ook nog prima. (vandaar; lichte sauternes ...) – oh en een salade met cajunkip kan ook ...

Étoiles du Nord, voor uw betere wijnen...
Al is het alleen maar door Il Respiro del Vino te kunnen lezen; geen vertaling tot nu toe dan maar zwoegen.
Le Chardonnay rose est une mutation du Chardonnay blanc que l’on trouve historiquement à l'état de ceps isolés dans les vignobles champenois et bourguignons. La mutation porte principalement sur la couleur de la baie qui est d’un rose foncé à maturité. Cette différence a abouti à la proposition d’individualiser le Chardonnay rose comme une variété distincte de sa forme blanche et de l’inscrire en tant que telle au Catalogue français.

L’origine de ce cépage est difficile à dater. Néanmoins, il existe quelques repères comme la date de son introduction dans la collection de Vassal-Montpellier en 1950 ; deux accessions (ou "introduction" est un clone non agréé conservé dans une collection) de Chardonnay rose y ont été plantées cette année-là. La première, issue de l'ancienne collection dite "de Ravaz" de l'Ecole de Montpellier (donc la date réelle est antérieure à 1950), provenait initialement de la Côte d'Or. La deuxième provenait de la "collection Couvreur Pernin", à Rilly-la-Montagne dans la Marne.
Depuis peu, le Domaine de Vassal-Montpellier possède également deux accessions assainies issues du clone de Rilly-la-Montagne. Récemment de nouvelles accessions de Chardonnay rose ont été recensées dans le vignoble champenois, preuve d’un intérêt croissant pour ce cépage ancien. Cependant, la disparition progressive des veilles vignes ainsi que la pression croissante des viroses, faisaient craindre la perte de diversité génétique au sein de ce cépage et l’abandon de sa culture.
Zie deze voor andere benamingen bij een andere leverancier.